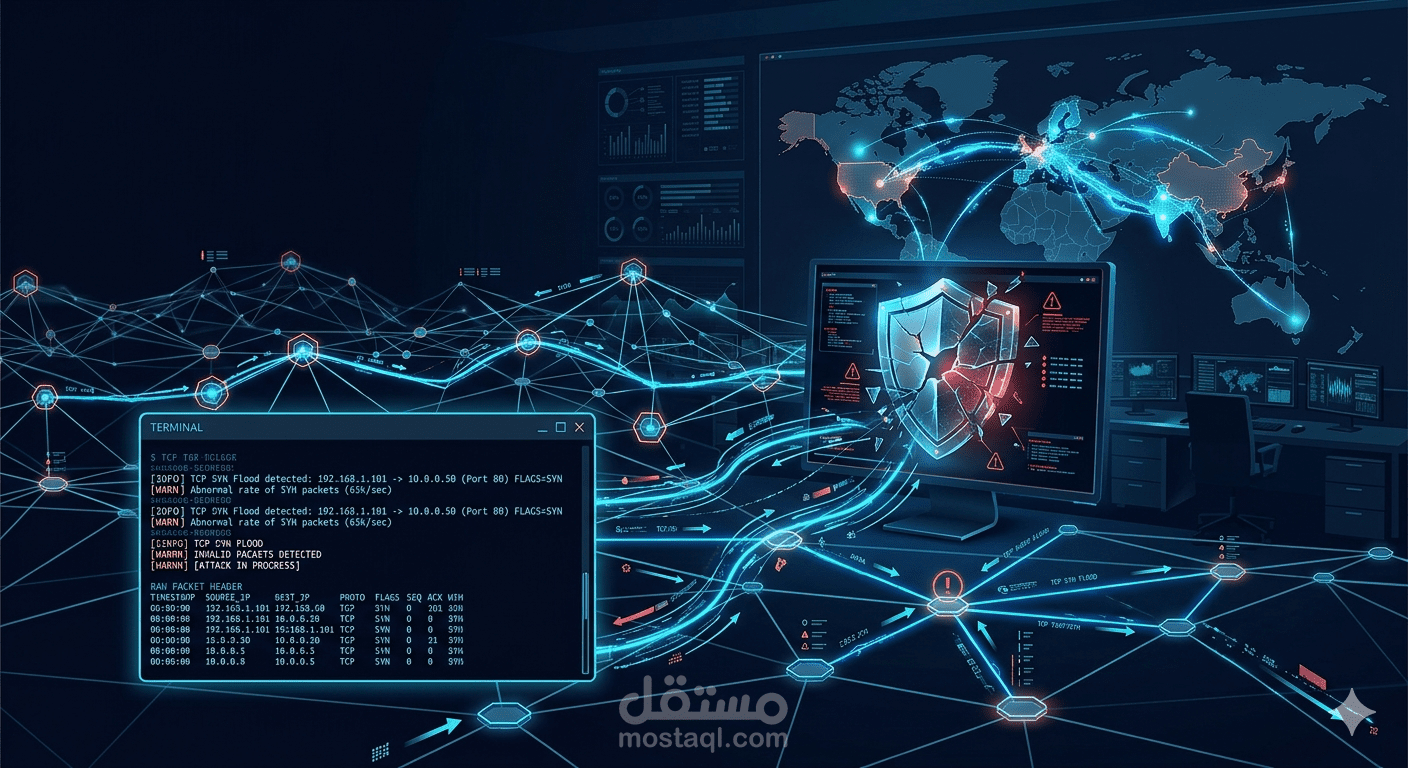
TCP/IP Attacks
تفاصيل العمل
SEED Lab — TCP/IP Attack Lab Project
This project is based on the SEED Security Labs framework developed by Syracuse University, one of the most recognized hands-on cybersecurity education platforms worldwide.
The lab explores real exploitation techniques targeting fundamental weaknesses in the TCP/IP protocol suite — vulnerabilities that exist by design, not misconfiguration.
The project covers four documented attacks:
SYN Flood Attack — Launching a DoS attack using raw packet crafting to exhaust a server's half-open connection queue
TCP RST Attack — Terminating active connections between victims by forging RST packets with correct sequence numbers
TCP Session Hijacking — Injecting malicious commands into an active Telnet session by predicting sequence numbers
Reverse Shell via Hijacking — Escalating session hijacking into full remote shell access on the victim machine
All attacks are executed inside a controlled virtual network using tools like Scapy, Netwox, and Wireshark — the same toolset used in professional penetration testing.
This project demonstrates a deep practical understanding of how TCP/IP works at the packet level, moving beyond theory into real exploit execution and traffic analysis — directly aligned with skills required in penetration testing, red teaming, and network forensics