ASA Firewall Implementation Project
تفاصيل العمل
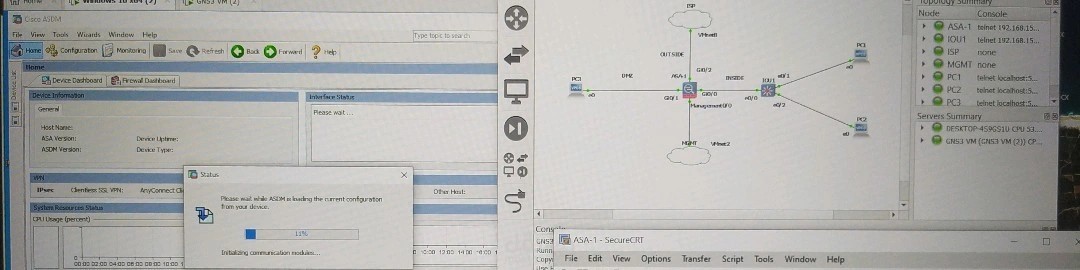
## What I Built:
- **Multi-Zone Security Architecture** - INSIDE/DMZ/OUTSIDE zones with granular security policies
- **Advanced NAT Implementation** - Dynamic PAT and static NAT for DMZ services
- **Comprehensive Access Control** - Zone-based ACLs with least-privilege principles
- **Secure Management Infrastructure** - SSH, HTTPS (ASDM), and role-based authentication
- **Enterprise Network Services** - DHCP server with DNS integration
- **Traffic Flow Analysis** - Real-time monitoring and security event logging
## Key Technical Achievements:
- Deployed ASAv 9.16(2)14 in a virtualized GNS3 environment
- Configured three-tier security model with appropriate security levels (100/50/0)
- Implemented object-based NAT policies for scalable network address translation
- Established secure remote access with RSA 2048-bit encryption
- Created comprehensive documentation following enterprise standards
## Real-World Impact:
This wasn't just another lab exercise. The architecture I designed mirrors actual enterprise deployments I've analyzed, addressing genuine security challenges like:
- DMZ server protection with controlled external access
- Internal network segmentation and traffic filtering
- Secure administrative access for remote management
- Scalable DHCP services with proper DNS configuration
## What's Next:
Currently diving deeper into advanced threat protection and exploring integration with SIEM platforms. The foundation I've built here opens doors to implementing next-gen security features like IPS/IDS and advanced malware protection.
Huge thanks to Dr. Sara Ahmed Soliman and my supervisor Sara Mohamed Shebl at HTI for their guidance throughout this challenging project. The hands-on experience gained here is invaluable for my cybersecurity career trajectory.
**Fellow network security enthusiasts** - what's been your most challenging firewall implementation? Would love to hear about your experiences with enterprise security architectures!