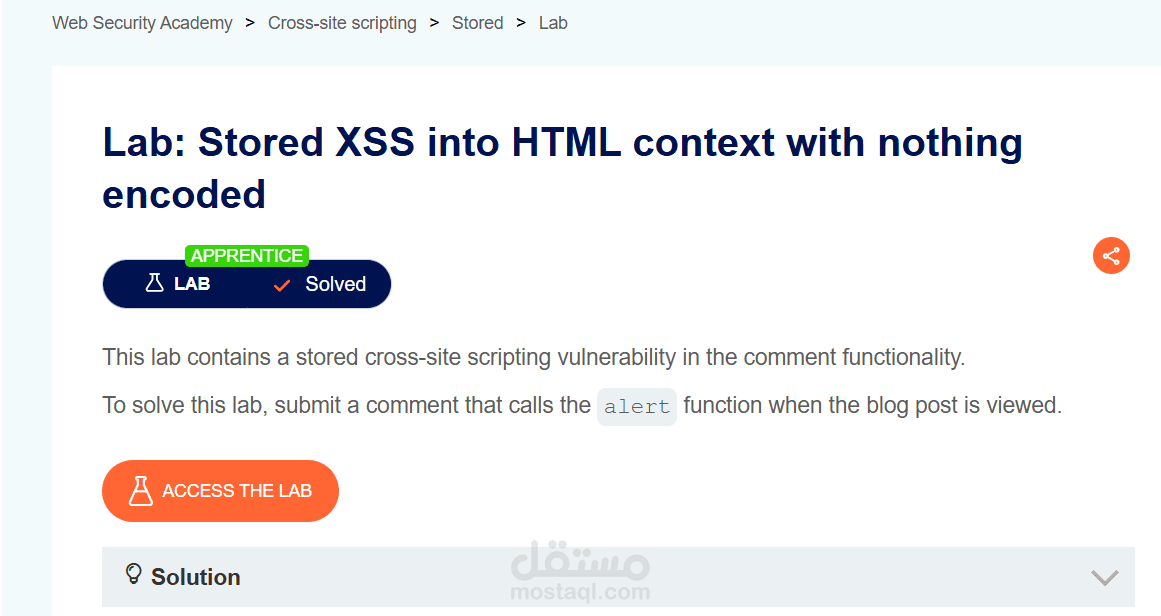
Stored XSS into HTML context with nothing encoded
تفاصيل العمل
Successfully identified and exploited a Stored Cross-Site Scripting (XSS) vulnerability in an HTML context within a web application testing lab.
The vulnerability occurred because user input was stored by the application and later rendered in the HTML page without proper sanitization or encoding. By injecting a malicious JavaScript payload, the script was permanently stored on the server and executed automatically whenever a user viewed the affected page.
This demonstrates how attackers can persistently execute malicious scripts affecting multiple users interacting with the application.
الأدوات المستخدمة
Burp Suite
Browser Developer Tools
ما تم تنفيذه
Identified input fields that store user data in the application database.
Injected a malicious JavaScript payload into the stored input field.
Confirmed that the payload executed whenever the page was loaded.
Analyzed the impact of persistent XSS on user sessions and application security.
التأثير الأمني
This vulnerability could allow attackers to execute malicious JavaScript in the browsers of multiple users, potentially leading to session hijacking, credential theft, or malicious actions performed on behalf of victims.