Splunk deployment for log analysis and monitoring
تفاصيل العمل
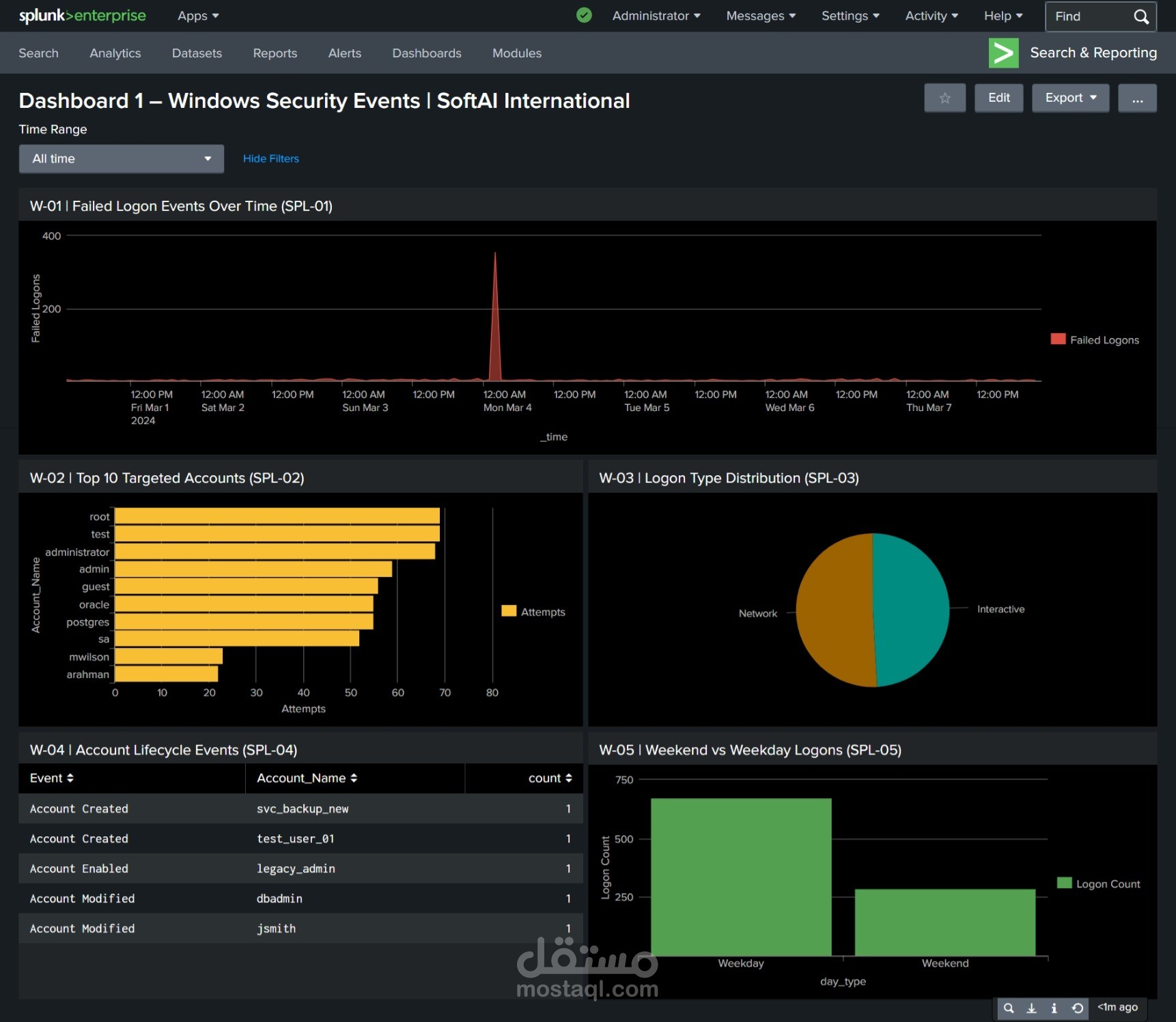
Splunk SIEM Deployment — SoftAI International
Overview
Deployed a full Splunk Enterprise SIEM solution for SoftAI International covering 5 log sources, 85,885 events, and a 7-day active monitoring window.
What I Did
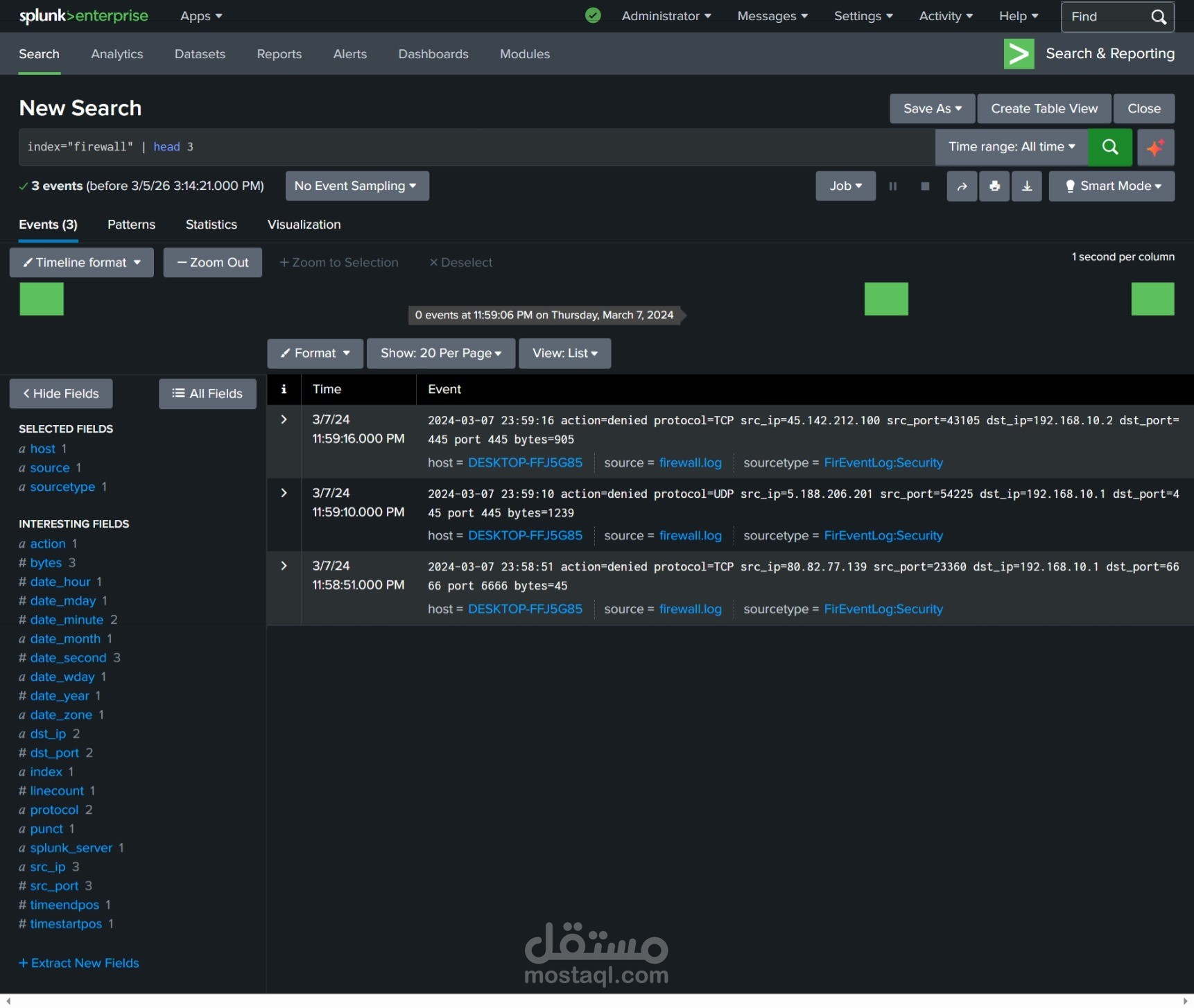
Designed and ingested 5 log datasets into dedicated Splunk indexes: Windows Security, Linux Authentication, Apache Web Access, Cisco Firewall, and Application Performance.
Wrote 25 SPL queries using timechart, stats, eval, rex, dc(), where, avg() covering the full detection lifecycle.
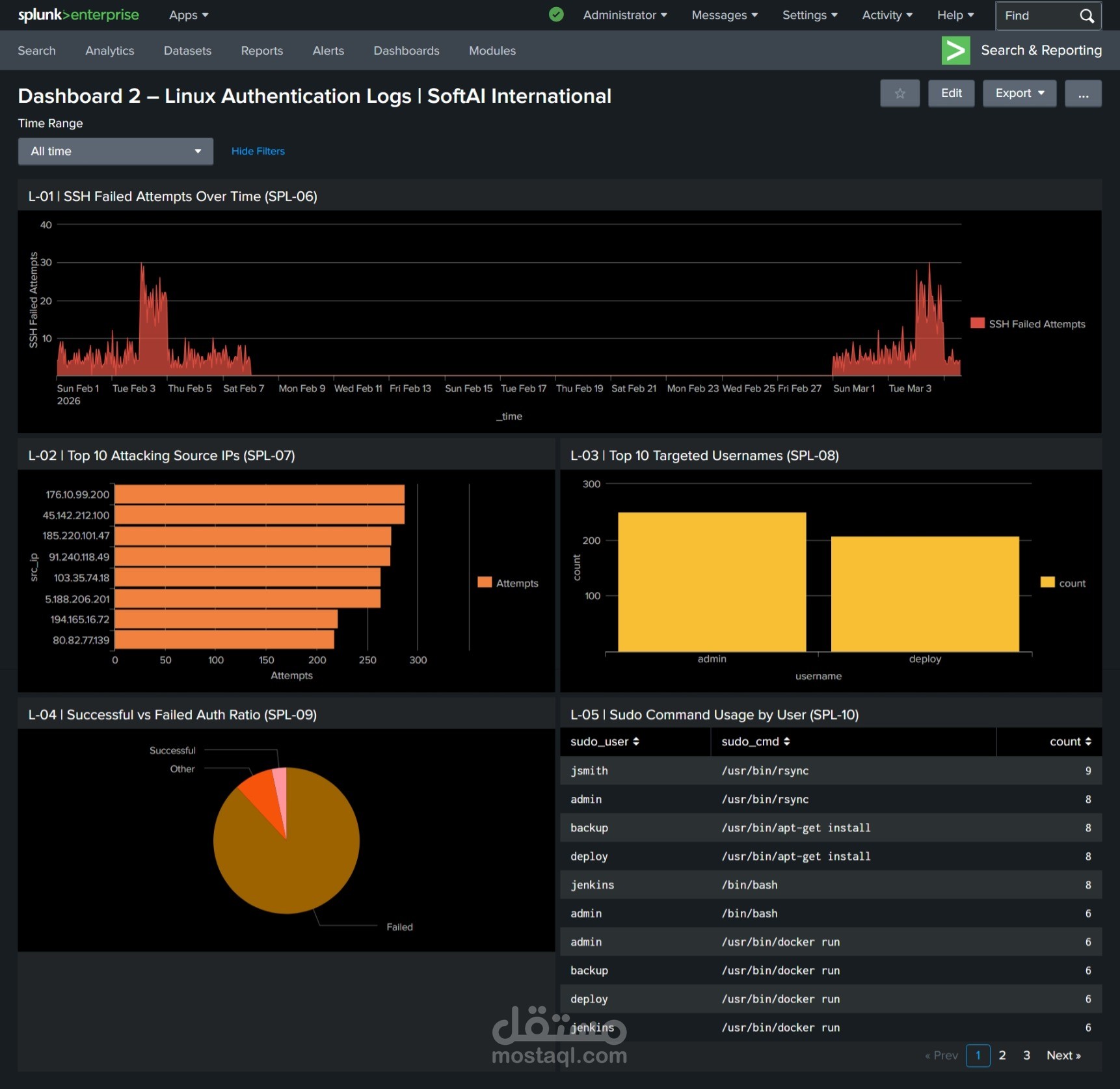
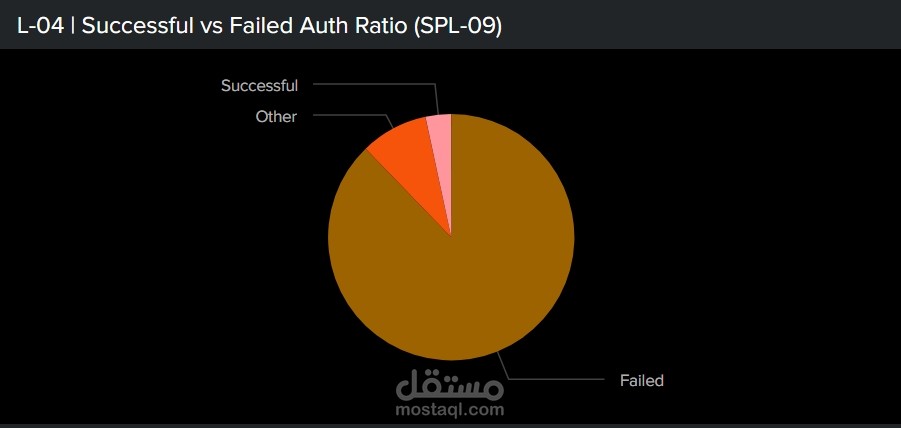
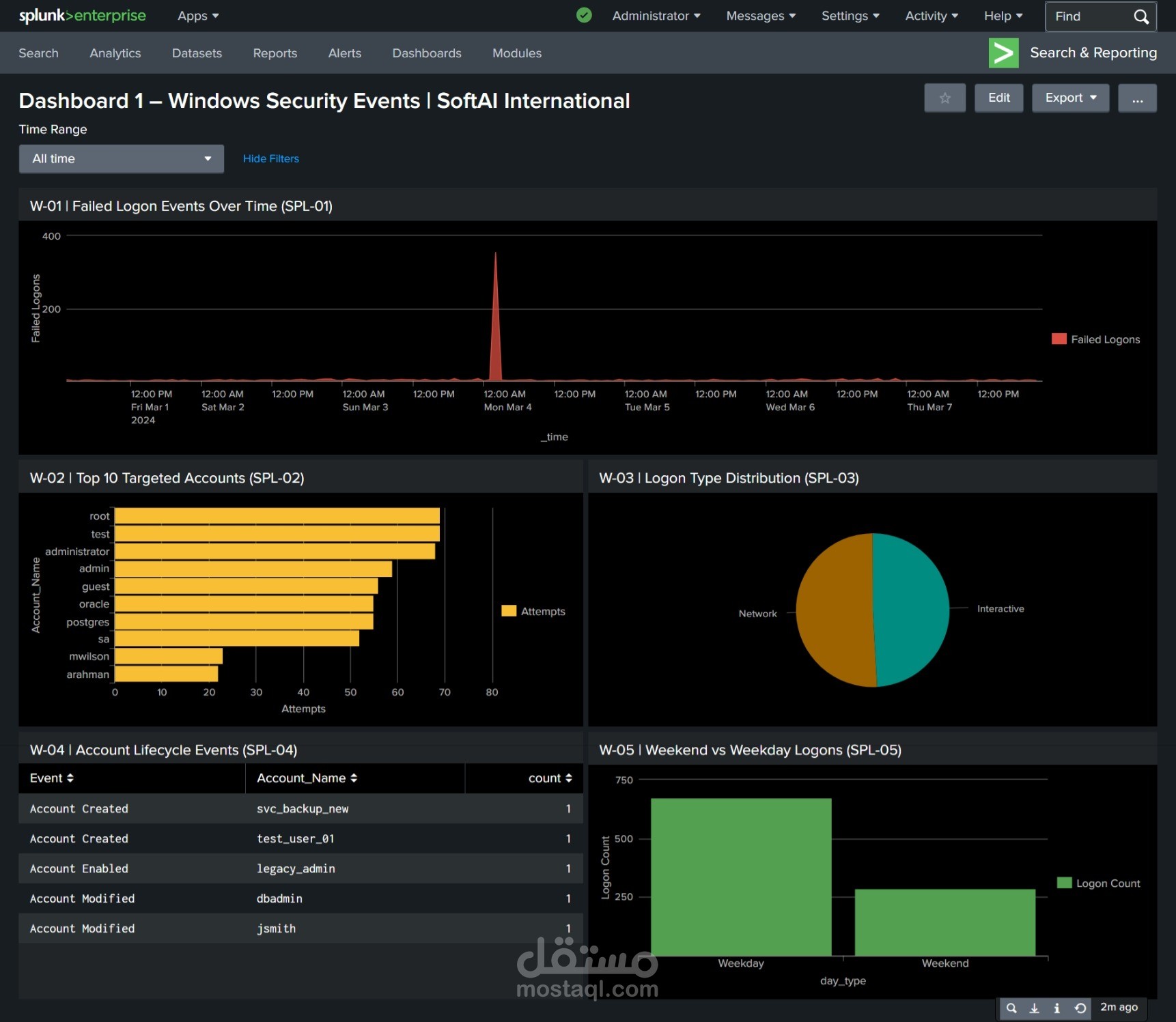
Built 5 interactive dashboards (25 panels total) with dark-theme SOC-style visualisations.
Deployed syslog-ng real-time TCP log forwarding between two Linux nodes with near-instantaneous delivery.
Configured automated Splunk alerting for SSH brute-force threshold breach detection.
Key Findings
Detected a brute-force burst of ~350 failed Windows logons in an 8-second window on 4 March 2024 02:00.
Identified IP 45.142.212.100 scanning 506 unique destination ports with 4,333 total firewall attempts.
Linked the same threat actor IPs across Apache, Linux, and firewall logs using cross-dataset correlation.
Web reconnaissance confirmed against /phpMyAdmin/, /.env, and /wp-login.php from 2 external hosts.
Tools & Technologies
Splunk Enterprise, SPL, syslog-ng, Windows Event Logs, Linux auth.log, Apache access.log, Cisco ASA Firewall Logs, Application Performance Logs.