NTI المنوفيه
تفاصيل العمل
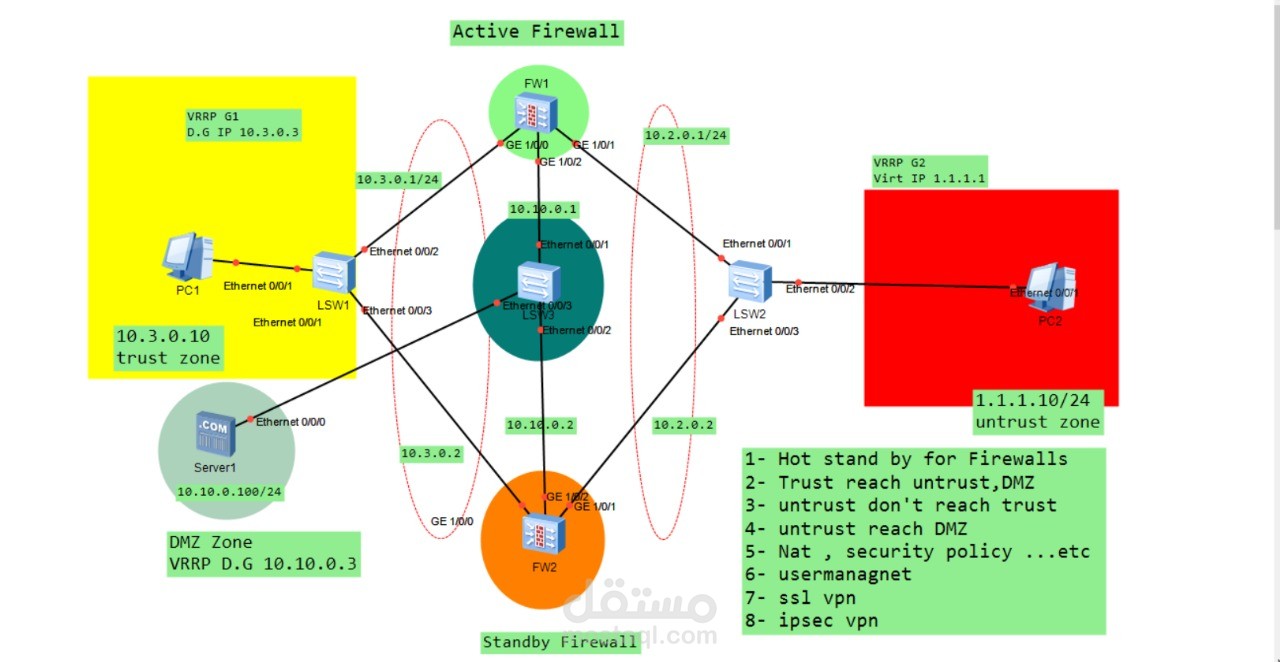
Secure Network Infrastructure Design with High Availability Firewalls
This project demonstrates the design and implementation of a secure enterprise network architecture using dual firewalls configured in a High Availability (Hot Standby) setup to ensure network reliability and continuous service availability.
The network is divided into three main security zones to enhance security and traffic control:
1. Trust Zone (Internal Network)
This zone represents the internal company network where employee devices are located. It includes client machines such as PC1 operating in the 10.3.0.0/24 subnet. The default gateway is configured using VRRP to provide gateway redundancy.
2. DMZ Zone (Demilitarized Zone)
The DMZ hosts public-facing services such as servers that need to be accessible from external networks while remaining isolated from the internal network. In this design, Server1 operates in the 10.10.0.0/24 subnet and is protected by the firewall layer to prevent direct access to the internal network.
3. Untrust Zone (External Network / Internet)
This zone represents the external network or internet. A simulated external client (PC2) exists in the 1.1.1.0/24 subnet to test external connectivity and access policies.
To ensure network resilience, two firewalls are deployed:
FW1 – Active Firewall
FW2 – Standby Firewall
If the active firewall fails, the standby firewall automatically takes over, ensuring uninterrupted network operation.
The network design also implements multiple security and networking technologies including:
VRRP (Virtual Router Redundancy Protocol) for gateway redundancy
Network Address Translation (NAT) for internal-to-external communication
Security Policies to control traffic between zones
User Management for authentication and access control
SSL VPN for secure remote access
IPSec VPN for secure site-to-site connectivity
Traffic policies are configured to allow internal users to access the internet and DMZ services, while preventing unauthorized external access to the internal network, ensuring a secure and segmented network architecture.
This design focuses on network segmentation, high availability, and enterprise-level security implementation.