FortiGate Firewall Configuration: DNAT, IPsec VPN & Security Policies (FGT1 & FGT2)
تفاصيل العمل
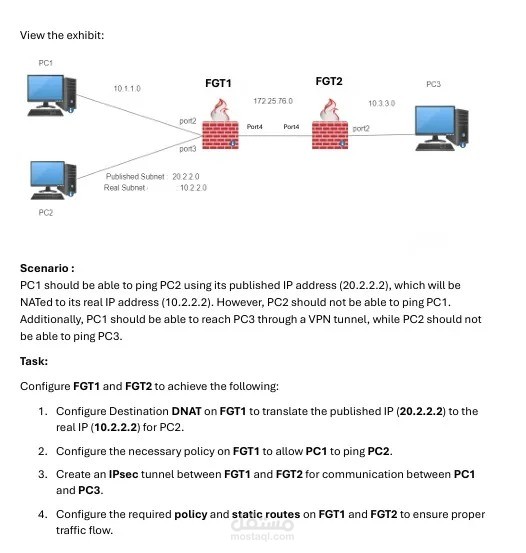
Configured a dual-FortiGate network environment involving Destination NAT (DNAT), IPsec VPN tunnel, and security policies to control traffic flow between multiple network segments.
Key tasks completed:
Configured DNAT on FGT1 to translate a published IP (20.2.2.2) to a real internal IP (10.2.2.2)
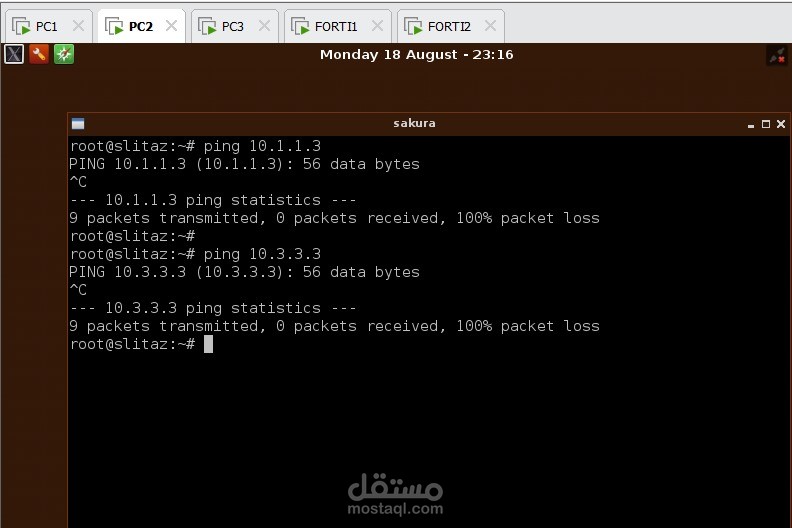
Created firewall policies to allow selective ping access between PC1 and PC2
Established a site-to-site IPsec VPN tunnel between FGT1 and FGT2 for PC1–PC3 communication
Configured static routes on both firewalls to ensure correct traffic flow
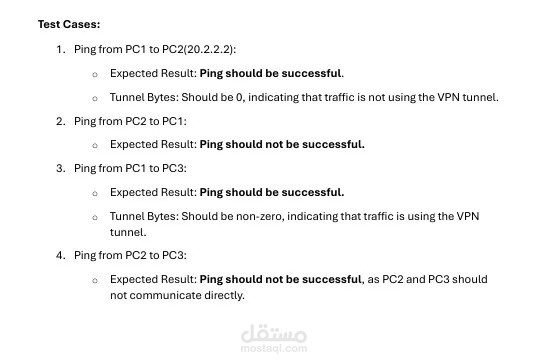
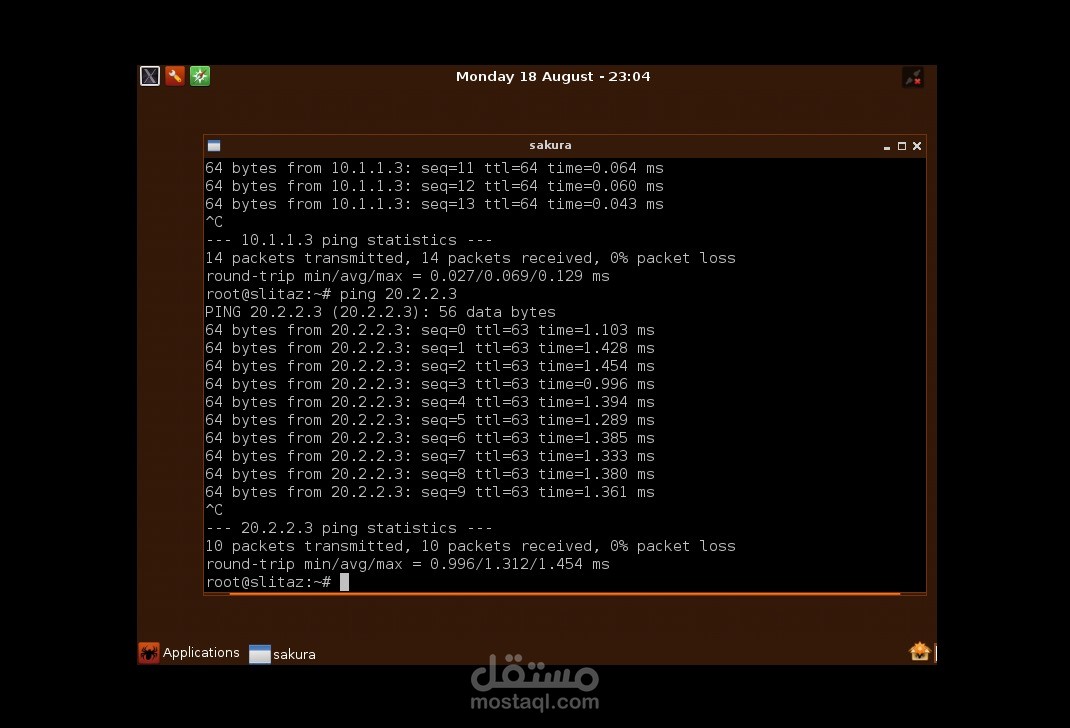
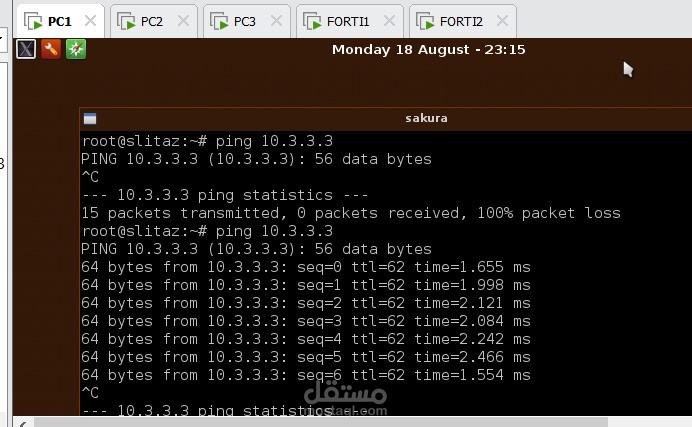
Verified results through test cases (ping tests + tunnel byte validation)