Leveraging Honeypots and Machine Learning for Network Intrusion Detection and Prediction
تفاصيل العمل
The world of cybersecurity is constantly evolving, with cyberattacks becoming increasingly sophisticated and difficult to predict. As technology advances, so do the methods used by cybercriminals to infiltrate systems and steal sensitive data? In this study, we explore the challenges of staying ahead of these threats and the potential benefits of using honeypots to collect real-time attack data.
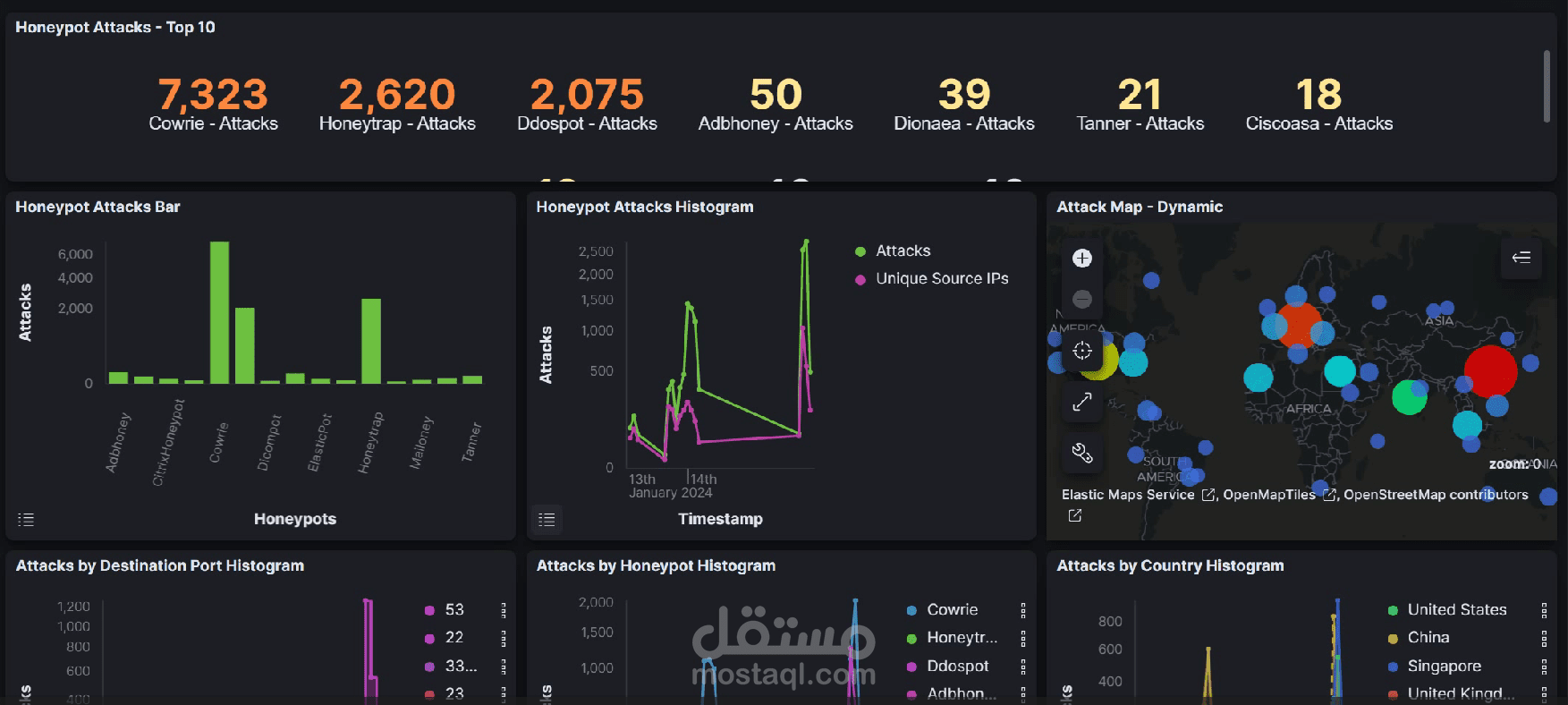
Honeypots, such as the T-Pot system which a framework of honeypots developed by German telecommunications company of Deutsche Telekom, are designed to mimic vulnerable systems and attract cybercriminals, allowing security experts to monitor and analyze their behavior. By collecting data on the tactics and techniques used by attackers, honeypots can provide valuable insights into the latest trends and threats in the field of cybersecurity.
One promising application of honeypot data is the creation of machine learning models for proactive threat identification and mitigation. By training these models on real-world attack data, security experts can develop more effective strategies for preventing and responding to cyberattacks. This approach has the potential to revolutionize cybersecurity measures and provide organizations with a more proactive and effective defense against cyber threats.
In this paper, we examine the benefits of using honeypots to collect real-time attack data and the potential to develop a machine-learning model to improve cybersecurity measures.